What are sneaker bots? How do they work? Are they illegal? And how can sneaker retailers prevent bots? Read on to find out everything you need to know about sneaker botting.
Table of contents
A sneaker bot, also known as a “shoe bot”, is software that’s designed to help purchase sneakers by performing automated tasks like entering raffles, completing checkouts, and checking for inventory.
Sneaker bots imitate the behavior of human users, only faster and in larger volumes. This means these shoe bots can unfairly find and purchase sneakers in ways human customers can’t.
Sneaker bots use software to execute automated tasks based on the instructions bot makers give them. Because they're just software programs, shoe bots can help resellers buy sneakers in many different ways.
On the simpler end, there are automated bots that scrape inventory information from a web page. For example, you could set up a bot to regularly check a product page, then automatically alert you when new stock becomes available.
On the more complex end, there are sneaker bots that inject pre-recorded mouse and click behavior from human users to fool sophisticated bot mitigation software.
Bot operators go to great lengths to cover their tracks. The more sophisticated reseller bots use proxies and VPNs to mask their IP addresses, for example. This makes it appear as if the bots are coming from unconnected, individual residential addresses instead of one coordinated address.
Sneaker bots go by many names: AIO bot, KodaiAIO, NikeShoeBot, and GaneshBot are just a few. Some are even custom-made to target certain retailers, like Foot Locker, Nike, or Adidas.
The best way to group sneaker bots is based on their functions.
Some bots have just one. Some have several. Here’s the most common types of sneaker bots and how they work.
Do you have a bot problem? Get your free guide to uncover the risks of bots & discover how you can beat them

 Scraping bots
Scraping bots
Like we saw above, scraping sneaker bots work by monitoring web pages to facilitate online purchases. These bots could scrape pricing info, inventory stock, and similar information. They can be set up to automatically alert a bot operator when a sneaker drops or is restocked.
Here we can see the unfairness of sneaker bots.
Imagine a sneakerhead wanting to compete with this bot. The sneakerhead would need to sit at her computer, manually refresh the browser, and stare at her screen 24/7 until the restock happens.
She could only keep this up for a few hours. And what if the restock happens when she’s having lunch or using the bathroom?
Scraper bots don’t eat. They don’t take breaks. And they don’t tire out.
Humans have no chance to compete with them.
 Footprinting bots
Footprinting bots
Footprinting is like scraping, but involves the bot probing and scanning the website. For example, a footprinting bot could search for live web URLs that haven’t yet been made public.
Footprinting bots were the culprits behind the cancelled Strangelove Skateboards x Nike SB Dunk Low collaboration.
Strangelove wrote that “the raging botbarians at the gate broke in the back door and created a monumental mess for us this evening… We regret to inform everyone that tomorrow’s launch has been cancelled and we will not be selling them on the site.”
The footprinting sneaker bots found product page and purchased the products a day before the release even happened.
 Account creation bots
Account creation bots
For bot operators to finalize purchases, they often need an account with the retail site. They can generate a list of free emails and then use an account creation bot to create hundreds or thousands of accounts in bulk.
RELATED: Detect & Block Bots To Serve Real Customers
 Account takeover bots
Account takeover bots
Instead of creating new accounts from scratch, bad actors sometimes use bots to access other shoppers’ accounts.
Both credential stuffing and credential cracking bots do multiple login attempts with (often stolen) usernames and passwords.
In a credential stuffing attack, the bot will test the list of usernames and passwords to see if they allow access to the sneaker retailer’s site.
A credential cracking bot will start with one value, maybe an email, and then test different password combinations until the login is successful.
 Scalping bots
Scalping bots
Scalper bots, also known as resale bots or reseller bots, are probably the most well-known kind of bots for sneaker drops.
Scalper bots use their speed and volume advantage to clear the digital shelves of sneaker shops before real sneakerheads even enter their email address.
A typical scalper bot will “sit” on the sneaker product page, constantly refreshing to click “add to cart” the second the sneaker drops. It’ll let the bot operator complete any CATPCHA tests, then zoom through the checkout process, autofill billing and shipping information, and press “buy” at lightning speed—as little as 0.2 seconds.
 Denial of inventory bots
Denial of inventory bots
Ever wonder how you’ll see sneakers listed on secondary markets like StockX or eBay before the kicks even drop? Denial of inventory bots are to blame.
A perfect example of sophisticated, next-gen bots, these bots add sneakers to online shopping carts and hold them there. They don’t buy them—at least not initially.
Holding sneakers in the cart denies other shoppers the chance to buy them. Often, discouraged sneakerheads will turn to resale sites and pay double or triple the MSRP to get what they couldn’t on the retailer’s site.
Only when a shopper buys the product on the resale site will the bot operator have the bot complete the purchase.
 Cashing out bots
Cashing out bots
Some bot operators don’t just use bots to put sneakers in shopping carts. They’ll also use cashing out bots to validate stolen credit card information and then use the bots to buy the products reserved by their scalping or denial of inventory bots.
RELATED: Why Major Sneaker Brands Are Running “Live Raffles” For High Heat Drops
Sneaker botting is the sneaker world’s term for using bots to buy shoes. Botting works by giving people better chances at purchasing high-value sneakers, which are often resold for profit on the secondary market.
Sneaker botting has evolved far beyond individual resellers flipping a few products on eBay—it’s become big business.
The estimated value of the global sneaker resale market is $10 billion.
There are sneaker reseller millionaires. Whole companies with dozens of employees who buy and resell sneakers. Resale marketplaces with multi-billion-dollar valuations.
In this market, bot developers have shifted from buying and reselling sneakers to creating and selling bots. They’ve scaled up operations to avoid dealing with listing products on marketplaces and handling huge volumes of inventory.
Today, the shoe botting ecosystem involves:
- Bots for sale: You can buy any number of bots directly from developers or on the secondary market.
- Cook groups: Paid membership groups (usually on Discord) with insider information and sneaker stock alerts.
- Bot-as-a-Service: Bot subscription services with employees, 24/7 support, and regular software updates.
- Add to cart services: Businesses you can pay to execute sneaker purchases for you.
- Secondary markets: Marketplaces with verification services, price trackers, auctions, and much more.
One analysis of a sneaker bot business estimated it makes just under $200k per year from its software sales and subscription services alone.
And Queue-it co-founder Niels Henrik Sodemann told Forbes, "We believe that there [are] at least a hundred organizations ... where people can sign up to get the access to the sneakers."
In the video below, CNBC interviews sneaker reseller "Botter Boy Nova", who claims he alone makes around $130k per year botting sneakers.
The short answer is no. There are currently no laws against using bots to buy sneakers.
If there were, "Botter Boy Nova" would almost certainly not have agreed to be interviewed by CNBC.
Now for the long answer.
First, using automated bots to buy sneakers often violates retailers' terms of sale. Some retailers, like Nike, include clauses in their terms of service that enable them to charge restocking fees, decline refunds, and suspend the accounts of people it determines are buying sneakers with the intent to resell them.
Second, botting sneakers may soon be illegal if the Stopping Grinch Bots Act is passed. This would make it unlawful “to circumvent a security measure, access control system, or other technological control or measure on an Internet website or online service to enforce posted purchasing limits or to manage inventory” (translation: it would make sneaker bots illegal).
Until then, it's up to retailers to stop bots from snatching sneakers out of the hands of genuine customers.
But what can retailers do to stop bots?
Let's find out.
If bots were easy to stop, someone would’ve done it by now.
Bot operators use cutting-edge methods of attack. As a sneaker retailer, your defenses need to be just as sophisticated.
In practice this means you need a combination of tools and strategies tailored to bots’ diverse attack vectors.
Here’s a list of some actions you can take to prevent sneaker bots from ruining your sneaker drops.
RELATED: Bot Mitigation: How To Detect & Stop Bots
1. Block known bot traffic
One telltale sign of bot traffic is outdated browser versions.
Real visitors should be using an up-to-date version of a browser, but bot scripts frequently run on outdated versions.
It's recommended to show CAPTCHAs to browsers not updated in 2 years, and to flat out block browsers that haven't been updated in 3 years.
|
|
CAPTCHA End of life over 2 years ago |
BLOCK End of life over 3 years ago |
|
Chrome version |
< 102 |
< 90 |
|
Firefox version |
< 100 |
< 88 |
|
Safari version |
< 15.4 |
< 14.1 |
|
Edge version |
< 102 |
< 90 |
Updated as of May 2025. Release version history is available for Chrome, Firefox, Safari, and Edge.
Traffic from data centers often comes from sneaker bots—in fact, 45% of all bad bots come from data centers. That’s almost double the amount that comes from residential IP addresses.
Scalpers and other bad actors can purchase server space in a data center and easily obtain hundreds of IP addresses.
That’s why data center IP blocking is crucial to stopping bots.
Some known data centers you can block include:
- Digital Oceans
- GigeNET
- OVH Hosting
- Choopa
- LLC data centers
You can hard-block or challenge suspicious traffic using Queue-it’s data center IP blocking feature.
With traffic challenging, visitors with a data center IP address will need to solve a CAPTCHA or Proof-of-Work before entering the waiting room.
With hard-blocking, visitors with a data center IP address will see a 403 forbidden HTTP error code and will be unable to enter the waiting room.
Just like with browser versions, the most sophisticated bots won’t be making these mistakes. But you can take these decisive actions to cut down on low- to medium-sophistication bots.
2. Monitor traffic & identify bots
If you can’t measure it, you can’t improve it. So, if you don’t have tools to monitor and identify sneaker bot traffic, you’ll never stop it.
Professional bot mitigation software analyzes behavioral indicators like mouse movements, frequency of requests, and time-on-page to identify suspicious traffic. For example, if a user visits several pages without moving the mouse, it’s most likely a bot.
Bot mitigation software helps identify sneaker bots with digital fingerprinting. It looks at known information like browser type, IP address, cookies, browser extensions, and more to create a profile of users that can be flagged as suspicious.
Remember to look for bot mitigation solutions that monitor traffic across all channels—web site, mobile apps, and APIs. Sneaker bots can plug directly into retailer’s APIs to access products more quickly. You need to cover all entry points.
Finally, the best bot mitigation platforms use machine learning to constantly update to the threats on your specific web application. In the cat-and-mouse game of bot mitigation, your playbook can’t be based on last week’s attack.
RELATED: See More, Act Smarter: Get Full Insight into Your Bots & Abuse Problem
3. Act on flagged traffic with bot mitigation software
Once you’ve identified suspicious traffic, you need to figure out what to do with it.
Your bot mitigation software should let you test suspicious traffic through challenges, such as CAPTCHAs.
While sophisticated bots today can solve most CAPTCHAs, the challenge mechanism is still useful for quickly and easily blocking simple bots, such as scrapers. Many of our customers still use CAPTCHAs, and we still see sales in 2025 where millions of visitors fail the CAPTCHA challenge.
Queue-it's Proof-of-Work challenge targets bots attacking using volume by using computing power as the limiting factor for bots. It makes every visitors' device complete a computational challenge that's invisible to regular users, but overloads the devices of bot operators who are trying to get hundreds or thousands of spots simultaneously.
When you confirm visitors as bots, you need to tag and mitigate them. These actions range from blocking the bots completely, rate-limiting them, or redirecting them to decoy sites.
Logging information about these blocked bots can also increase your chances of preventing future attacks.
RELATED: Block Bots & Abuse with The Right CAPTCHA For You
4. Filter bots with a virtual waiting room
At airport security checkpoints, passengers are screened before they can proceed to their flight.
Similarly, a virtual waiting room acts as a checkpoint inserted between a web page on your website and the purchase path.
A virtual waiting room is uniquely positioned to weed out sneaker bots. It lets you run visitor identification checks and apply sophisticated access rules before visitors can buy their sneakers.
And it has the added benefit of providing a fair user experience during hyped sneaker releases.
All early visitors are gathered on a countdown page where hype builds.

When the sale starts, they’re randomized, just like a sneaker raffle.
Then anyone arriving after the start of the sale gets their place in line in a first-come, first-served order—the gold standard of fairness.
Ticketmaster, for instance, reports blocking over 13 billion bots with the help of Queue-it's virtual waiting room.
RELATED: Protect Against Bad Bots & Prevent Abuse With a Virtual Waiting Room

5. Allocate time for after-sale audits
Even with the most bulletproof bot blocking strategy, some sneaker bots will still get through.
But just because a bot made a purchase, it doesn’t mean the battle is lost.
Dedicate resources to review order confirmations before shipping the sneakers.
Review the orders and ask:
- Are there multiple orders shipping to the same address?
- Were several orders made using the same IP address?
- Was the same credit card used by different customers?
- Is there social media chatter from customers bragging about how they used bots to game your site?
If you identify known bot orders, cancel them and/or ban their account. You could also flag their address or credit card information for future releases.
These post-sale audits are why Nike changed their terms of service to include clauses that enable them to charge restocking fees, decline refunds, and suspend the accounts of people it determines are buying sneakers with the intent to resell them. It enables Nike to punish sneaker botters.
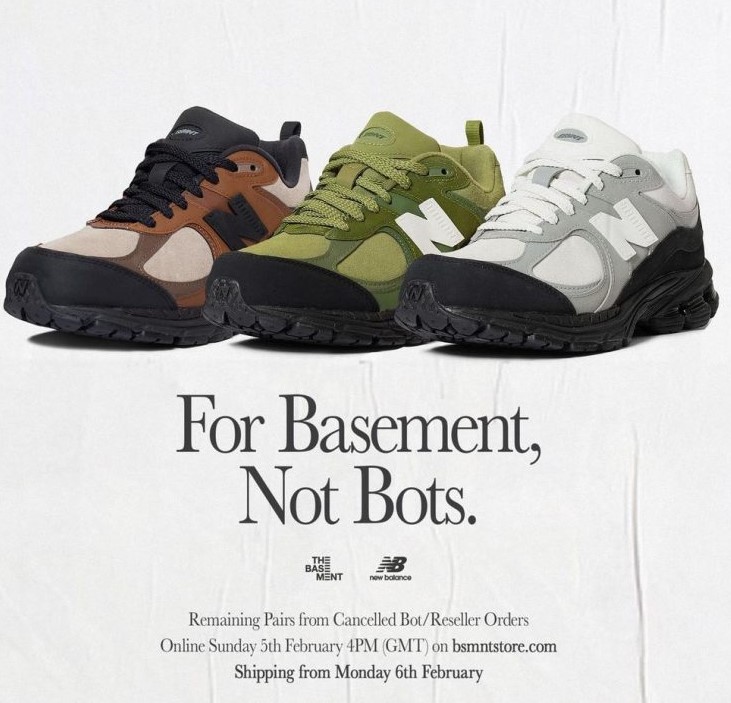
Another strategy is to "re-drop" the sneakers from the bot orders you've identified and cancelled, to show consumers you’re truly trying to keep releases fair.
The most advanced bot operators, however, work hard to cover their tracks.
They use rolling credit card numbers and residential proxies to obscure IP address and tweak shipping addresses—an industry practice known as “address jigging”—to fly under the radar of these checks.
But taking a critical eye to the full details of each order can help identify illegitimate purchases.
In the TechFirst podcast clip below, Queue-it Co-founder Niels Henrik Sodemann explains to John Koetsier how retailers prevent bots, and how bot developers take advantage of P.O. boxes and rolling credit card numbers to circumvent after-sale audits.
6. Run exclusive member-only sneaker drops
As long as there's profit to be made, resellers will do anything they can to bot shoes. In recent years, though, retailers have launched a new attack on botters by only offering high heat drop access to verified, genuine customers.
Nike CEO John Donahoe explains: “This approach sends personalized purchase offers to members based on their engagement with SNKRS, past purchase attempts, and other criteria, using data science to drive digital member targeting. For example, 90 percent of the invites for the Off-White Dunk went to members who had lost out on a prior Off-White collaboration over the past two years.”
Adidas also offers exclusive access via their “the invite” drop mechanism, which sends exclusive drop and restock purchase offers to their best customers.
The advantage of the invite-only strategy is that you choose who gets access to your drops. Bots can’t abuse your sales because they’re not invited to them.
Plus, you can use the exclusive drops to incentivize genuine customers to share their details and sign-up for your loyalty program or membership scheme.
To run large, exclusive drops, Queue-it customers use the Invite-only waiting room. They simply choose the customers to whom they want to grant access, send out invitations, then verify customer identities with two-factor-authentication.
The Invite-only waiting room lets you confidently keep bots out while rewarding your best customers and driving loyalty program sign-ups. It's already been used to block over 3 million bots during a large concert ticket sale, drive 50k loyalty program sign-ups during two hyped streetwear drops, and to give hundreds of thousands of loyal members across companies exclusive sale access.
RELATED: Roll Out the Red Carpet for VIP Customers with Exclusive Invite-only Sales & Drops
“Our members expect to get the benefits they pay for. Queue-it helped us deliver the exclusive drop access members were promised and gave us the peace of mind the website would be there for them.”
Tristan Watson, Engineering Manager

Sneaker bots are automated software programs designed to give their users a competitive advantage while shopping online.
To get this advantage, sneaker bots typically use speed and volume to make faster purchases and place more orders. But sneaker bots come in all shapes and sizes and are often designed to target a particular site (or even a particular drop).
Common types of sneaker bots include:
- Scraping bots
- Footprinting bots
- Account creation bots
- Account takeover bots
- Scalping bots
- Denial of inventory bots
- Cashing out bots
Sneaker botting has become a multi-billion-dollar industry, with whole businesses with hundreds of employees profiting off the sneaker resale market.
If you’re a sneaker retailer looking to bring fairness to your drops by blocking bots, you need to:
- Block known bot traffic
- Monitor traffic & identify bots
- Act on flagged traffic
- Filter bots with web traffic management
- Allocate time for after-sale audits
- Run exclusive, invite-only sneaker drops
